Firstly, my thoughts go out to everyone in Ukraine and to anyone that has friends and family there. I hope they are managing to keep safe.
Given that in the 20th Century we experienced 2 world wars, numerous regional conflicts that were proxies for, and could have escalated into, global conflicts, as well as countless civil wars and border disputes, to see a European country brazenly invade a neighbour based on patently untrue reasons is shocking. I sincerely hope the Russians come to their senses and cease this invasion ASAP.
In the run up to this invasion, several web commentators suggested that there would be an increase in cyber-attacks that occurred in parallel with the invasion on the ground. Based on the activity logs of several websites I have created and or manage; this seems to have commenced already.
WordPress sites are particularly at risk
I have identified concerted and extensive efforts to access websites that are noticeably different to the everyday attempts to login using a likely administrator username. You will understand if I don’t give any more details than this.
However, as the most widely used website development platform (by a considerable margin), it is not surprising if WordPress gets more attention.
I use Wix, Squarespace, Ionos, am I OK then?
Sadly not. Whilst WordPress accounts for the vast majority of websites developed using a Content Management System (and therefore attracts more attention from cyber-attackers), ANY website that has an ‘admin’ login of some sort is likely to come under attack.
Am I under attack from the KGB?
No. State organised cyber-attacks, should they occur, will focus upon major institutions such as banks, utilities, transport networks, government, and the military. Unless you work in one of these organisations / sectors then state organised cyber attacks are unlikely to impact you.
However, Russia has, as Wired Magazine puts it “An expansive web on nonstate actors, from cybercriminals to front organisation to patriotic hackers that it can and has leveraged to its advantage”. Moscow has habitually turned a blind eye to their activities so long as their focus has been outside of Russia. Their activities might not be directed specifically at your business or organisation but as the WannaCry malware cryptoworm outbreak in 2017 proved, collateral damage can spread far and wide. As a result of WannaCry, the NHS saw tens of thousands of computers infected, equipment such as MRI scanners out of action and postponed non urgent treatment for some patients. It is unlikely that the NHS was a primary target for this malware but once it got into their systems, it spread rapidly and with devastating impact.
Why do the attackers want to break into my website?
The cyber-attackers have numerous possible reasons for trying to access your site.
- To spread misinformation and propaganda
- For financial gain – e.g. Ransomeware where your site and data is held ‘captive’ until you pay for it to be released
- To connect with your users and followers (you may have very few, but they don’t know this)
- To attack other websites
- Malevolence – lets create even more disruption and unrest by defacing / taking down websites
What might a cyber-attacker do?
The first thing they will probably do if they gain access to your site, is change your password thus freezing you out. Other Administrators (if they exist) will be deleted to give them free rein to do whatever they like.
Your content may either be removed or amended to suit their objectives.
If you take payments for goods and services via your website, then most probably the beneficiary account will be switched so they take any future funds.
If you have a full eCommerce store on your site, you may find that your products are removed and replaced with goods that are under control of the cyber-attacker.
How do cyber-attackers break into websites?
They use a range of different methods.
- Brute force – they keep trying username and password combinations until they find one that works. These may have been harvested from previous data breaches and be sitting in huge databases available to purchase from the dark web.
- Via a known vulnerability. White and black hat hackers are continually testing the integrity of software. White hat hackers will inform the software developer so they can fix it, black hat hackers will sell details of the vulnerability to anyone that wants to exploit it.
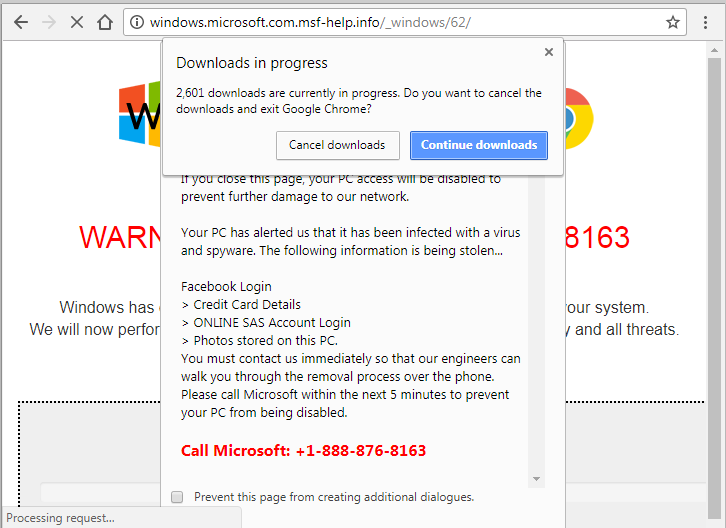
- Social Engineering. The easiest way to gain access to a website is to get someone to tell you their username and password. Cyber-attackers are exceptionally skilled in creating plausible approaches to website owners and administrators encouraging them to divulge usernames and or passwords. Be particularly suspicious of any request for a password reminder by another user on your site or a request by the ‘hosts’ for you to confirm the username and password for your site.
How can I protect myself / my website?
A few simple precautions will go a long way to helping to maintain the security of your site.
- Limit the number of users who have full Administrator rights to a minimum.
- Enforce strong username and password requirements for all users. For WordPress this should mean…
- Not using the default ‘admin’ username
- Setting the public display for authors names to NOT be their username
- Using long passwords – in excess of 15 characters
- Ensuring that any password used is unique to that site
- If it is available, consider using 2 Factor Authentication (2FA) when people login to the site.
- Put in place an application firewall or security tool. For WordPress, plugins like WordFence are a good place to start (though others are available). They are easy to install and even with the default settings, provide an enhanced level of security. The alerts and logs produced by these tools could give you enough warning that an attack is underway for you to step in and end it.
If you use another Content Management System (Drupal, Joomla etc), search for Security Extensions that will serve the same purpose. - Limit the number of failed logins and ban the IP address from where the login attempt originated. You ‘might’ inadvertently ban a legitimate user, but it is easy to unblock them if this occurs.
- Get and keep your site UPDATED. Cyber-attackers are on the look out for websites that are out of date and those which have known vulnerabilities in outdated software. Why make it easy for someone to break in by leaving a weakness unaddressed?
- Make sure you have a recent BACKUP of your site. Should the absolute worst happen, and your website be breached, knowing that you have a full and dependable backup you can revert to means that you have a level of insurance.
- If you only login in from one location (e.g. home or your office) consider restricting logins to only the IP address associated with that location.
Summary
Whilst you may believe that your website has little intrinsic value to a cyber-attacker, they may see it very differently. Your website is a platform for them to conduct a whole series of malicious and criminal activities IF they can access and take control of it.
Be vigilant to what is going on with your website. Even if you have no proof, assume your website is (or will be) under attack and act accordingly.
A few relatively simple steps can help to secure your website and give you peace of mind. Far better you act now to secure your site than spending hours (possibly days) trying to recover control, remove unwanted content, restoring the site and rebuilding your reputation.
If you have any concerns over the security of your site or believe you have experienced a cyber-attack, QD Design can help. Contact us for a free consultation.









 transactions should have alarm bells ringing loudly. No legitimate fundraising site would ask for payment to be made this way.
transactions should have alarm bells ringing loudly. No legitimate fundraising site would ask for payment to be made this way.






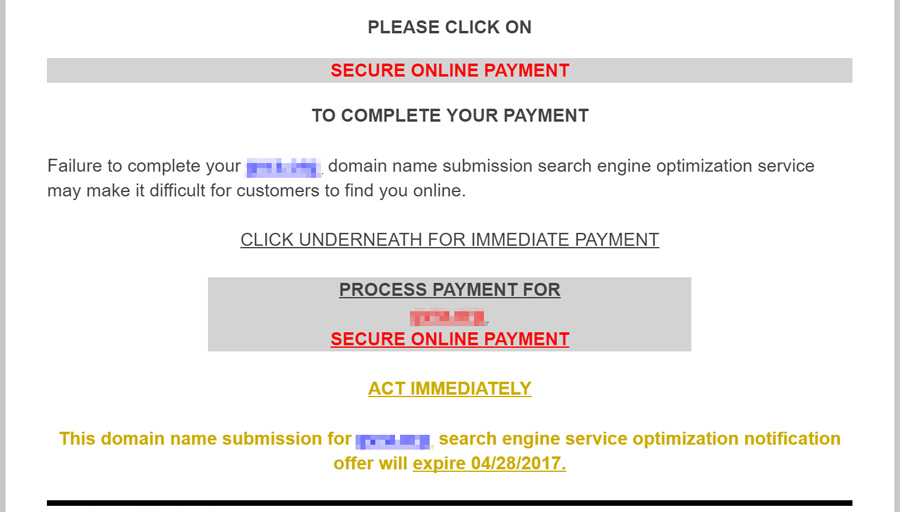

 When sending details of your credit card always look to see if
When sending details of your credit card always look to see if  Consider using a browser with the
Consider using a browser with the  Exercise caution when downloading new apps. Only download apps from trusted sources such as
Exercise caution when downloading new apps. Only download apps from trusted sources such as 